In today’s digital economy, your database is not just a backend system; it’s the heart of your business. From customer records to financial transactions, everything depends on how securely your data is stored, accessed, and managed. With cyber threats becoming more advanced and relentless, UK businesses can no longer rely on reactive security. What they need is advanced database protection that never sleeps.
Why Database Security Is Mission-Critical in the UK
With strict regulations like GDPR, ISO 27001, and PCI-DSS, organisations across the UK must maintain the highest standards of data protection. A single breach can lead to regulatory penalties, financial loss, and reputational damage that’s hard to recover from.
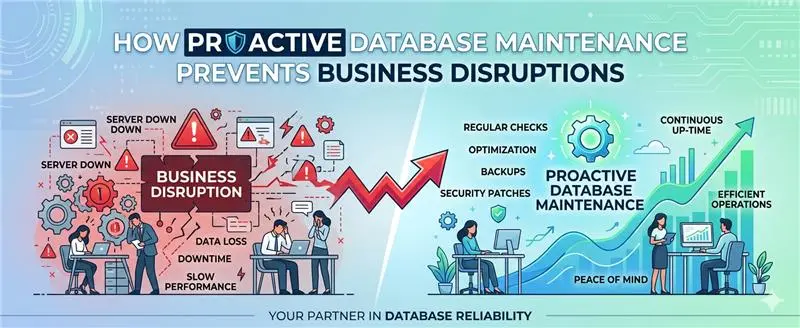
This is where managed database security services come in, offering a proactive, always-on approach to safeguarding your data infrastructure.
24/7 Managed Security Services: Protection Without Pause
Outsourcing your database security operations ensures that your systems are continuously monitored, maintained, and protected without burdening your internal teams.
With SLA-backed services, you get:
- Round-the-clock monitoring and threat detection
- Monthly health and threat intelligence reports
- Proactive patching and system updates
This ensures your databases stay resilient, optimised, and secure day and night.
Compliance Management & Audit Readiness
Staying compliant isn’t just about ticking boxes, it’s about building trust and avoiding costly penalties.
A robust database security strategy includes:
- Regular audit reports for full visibility
- Compliance alignment with GDPR, HIPAA, ISO 27001, and PCI-DSS
- Data masking and anonymisation for sensitive information
With expert guidance, your business remains audit-ready at all times.
Threat Detection & Real-Time Monitoring
Cyber threats don’t wait, and neither should your defence. Advanced monitoring systems help you:
- Detect unauthorised access attempts instantly
- Prevent SQL injections and suspicious activity
- Use behavioural analytics to identify anomalies
- Trigger automated alerts and rapid incident response
This real-time visibility allows you to stop threats before they escalate.
Vulnerability Assessments & Risk Audits
Even the most secure systems can have hidden weaknesses. Regular assessments help uncover them before attackers do.
Key components include:
- Identifying patch gaps and outdated systems
- Detecting misconfigurations that expose vulnerabilities
- Conducting penetration testing to simulate real-world attacks
This proactive approach ensures your database environment remains hardened against evolving threats.
Data Encryption & Access Control
Data security starts with controlling who can access your information and how they can access it. Modern database protection includes:
- Encryption of data at rest and in transit using AES-256 and TLS
- Role-Based Access Control (RBAC) to restrict user permissions
- Secure key management solutions
These measures ensure that even if data is intercepted, it remains unreadable and protected.
Zero Trust Architecture: Never Trust, Always Verify
Traditional security models assume everything inside the network is safe, but that’s no longer true.
A Zero Trust approach ensures:
- Strict identity and access management enforcement
- Least privilege access: users only get what they absolutely need
- Continuous validation of users and devices
- Segmentation of database access paths to limit exposure
This model protects your database from both external attackers and internal threats.
The Future of Database Security in the UK
As cyber threats continue to evolve, so must your defence strategy. Businesses that invest in proactive, intelligent, and fully managed database security services gain a significant advantage not just in protection, but in performance, compliance, and customer trust.
Final Thoughts
Database security is no longer optional; it’s a business necessity. With 24/7 monitoring, real-time threat detection, compliance assurance, and zero trust architecture, you can build a database environment that’s not only secure but future-ready.
If your current setup is reactive, it’s time to upgrade to a security model that never sleeps.